CYBERSEC 2022 uses cookies to provide you with the best user experience possible. By continuing to use this site, you agree to the terms in our Privacy Policy. I Agree
Cymetrics Info
Founded in 2021, Cymetrics is the cybersecurity brand under AIFT (formerly known as OneDegree Group), a group of innovative businesses with a strong presence in the APAC and Middle East regions.
From on-demand cybersecurity assessments to Red Team services, Cymetrics strengthens enterprise cyber defenses with proprietary SaaS-based technology and market-leading intelligence. Also, Cymetrics collaborates with its sister brand Vulcan to provide GenAI security, safety & compliance tools, from vulnerability assessment to protection.
Excelling in international CTF competitions, Cymetrics has achieved a top-three global ranking and secured 1st place in the prestigious 2024 HITCON Cyber Range blue team competition.
With ISO27001 and ISO27017 certifications, and as a Microsoft and AWS certified partner, Cymetrics has served 100+ clients across Asia in diverse sectors, including the public sector, financial services, Web3, technology, manufacturing, retail, e-commerce, and healthcare.
Contact Representative
- Name: Lisa Lin Product Marketing Manager
- TEL: 02-89352870
- E-Mail: lisa.lin@cymetrics.io
Products

Cymetrics is a comprehensive cybersecurity assessment SaaS platform to help our clients enhancing their visibility of the cyber exposures and managing the cyber risks with agility and flexibility. Cymetrics's one-click assessment and on-demand consultancy can assist our client to manage cybersecurity in a modern and streamline way.
Cymetrics Integrated Solutions:
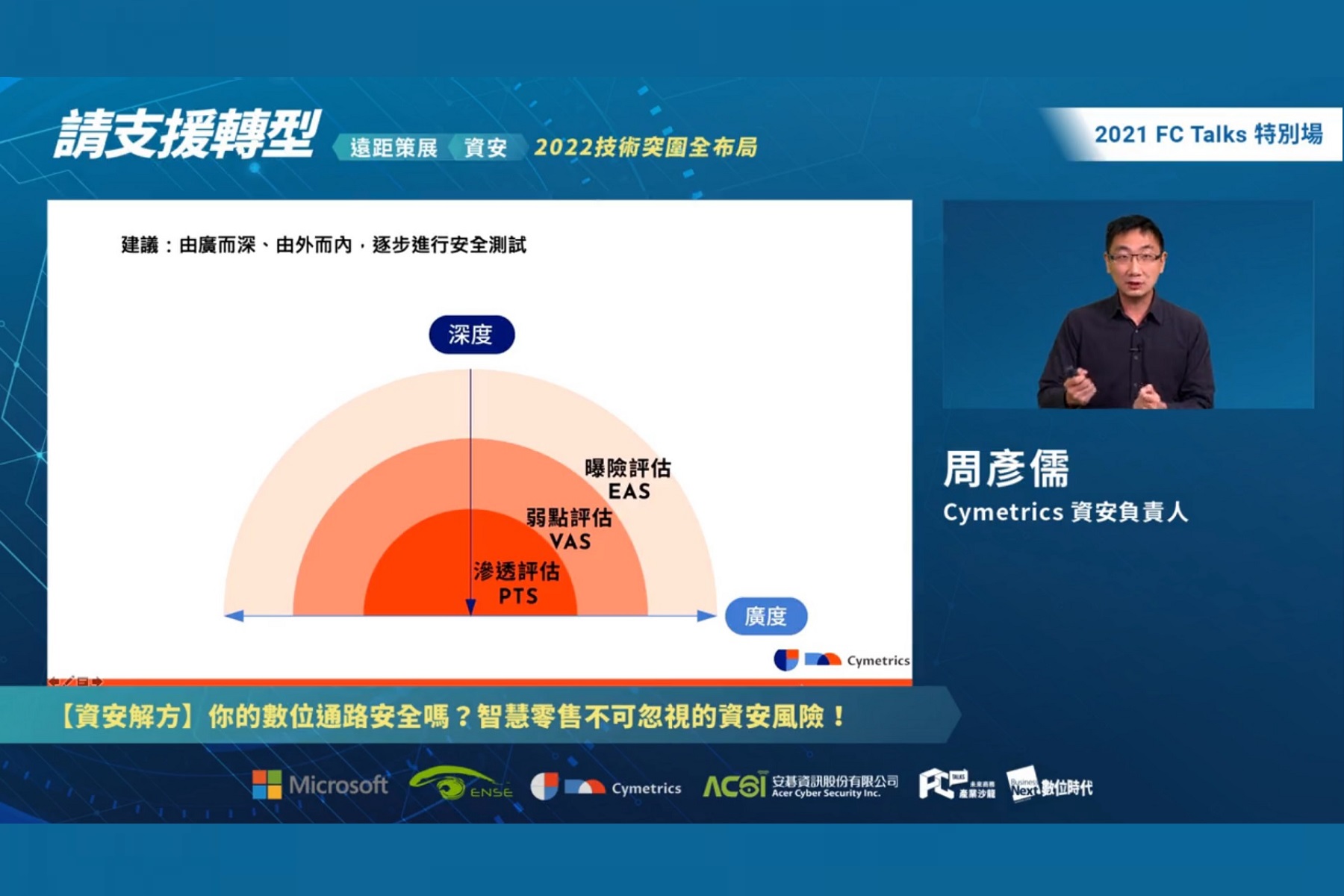
Level 1: Exposure Assessment as a Service (EAS)
By collecting and analyzing the external exposure information of clients, we help them start with understanding the risks within the organization and from the supply chain. We further conduct cybersecurity exposure management efficiently from the outside to the inside.
Level 2: Vulnerability Assessment as a Service (VAS)
We conduct detailed assessments based on various exposures. Our assessment items are performed by cybersecurity experts from the financial industry and cybersecurity engineers, based on the latest attack intelligence test scripts. Through proceeding the automatic and continuous vulnerability assessment by including the compliance from OWASP TOP 10, CWE and CVE, we also help clients to manage their own cybersecurity exposures before hackers do.
Level 3: Penetration Test as a Service (PTS)
Our qualified CEH cybersecurity experts follow the OSSTMM methodology to detect "known and unknown vulnerabilities" for the testing scope and provide consulting services to assist clients in managing vulnerabilities based on risks. In addition to vulnerability scanning, the detection items also include system logic and zero-day vulnerabilities, helping clients to detect the effectiveness of in-depth defenses with more complete and in-depth detection.
Solutions
Level 1: Exposure Assessment as a Service (EAS)
Level 2: Vulnerability Assessment as a Service (VAS)
Level 3: Penetration Test as a Service (PTS)
Level 1: Exposure Assessment as a Service (EAS)
By collecting and analyzing the external exposure information of clients, we help them start with understanding the risks within the organization and from the supply chain. We further conduct cybersecurity exposure management efficiently from the outside to the inside.
Level 2: Vulnerability Assessment as a Service (VAS)
We conduct detailed assessments based on various exposures. Our assessment items are performed by cybersecurity experts from the financial industry and cybersecurity engineers, based on the latest attack intelligence test scripts. Through proceeding the automatic and continuous vulnerability assessment by including the compliance from OWASP TOP 10, CWE and CVE, we also help clients to manage their own cybersecurity exposures before hackers do.
Level 3: Penetration Test as a Service (PTS)
Our qualified CEH cybersecurity experts follow the OSSTMM methodology to detect "known and unknown vulnerabilities" for the testing scope and provide consulting services to assist clients in managing vulnerabilities based on risks. In addition to vulnerability scanning, the detection items also include system logic and zero-day vulnerabilities, helping clients to detect the effectiveness of in-depth defenses with more complete and in-depth detection.